Hours of Manual Work
to Minutes
Smart, seamless AI-powered access control
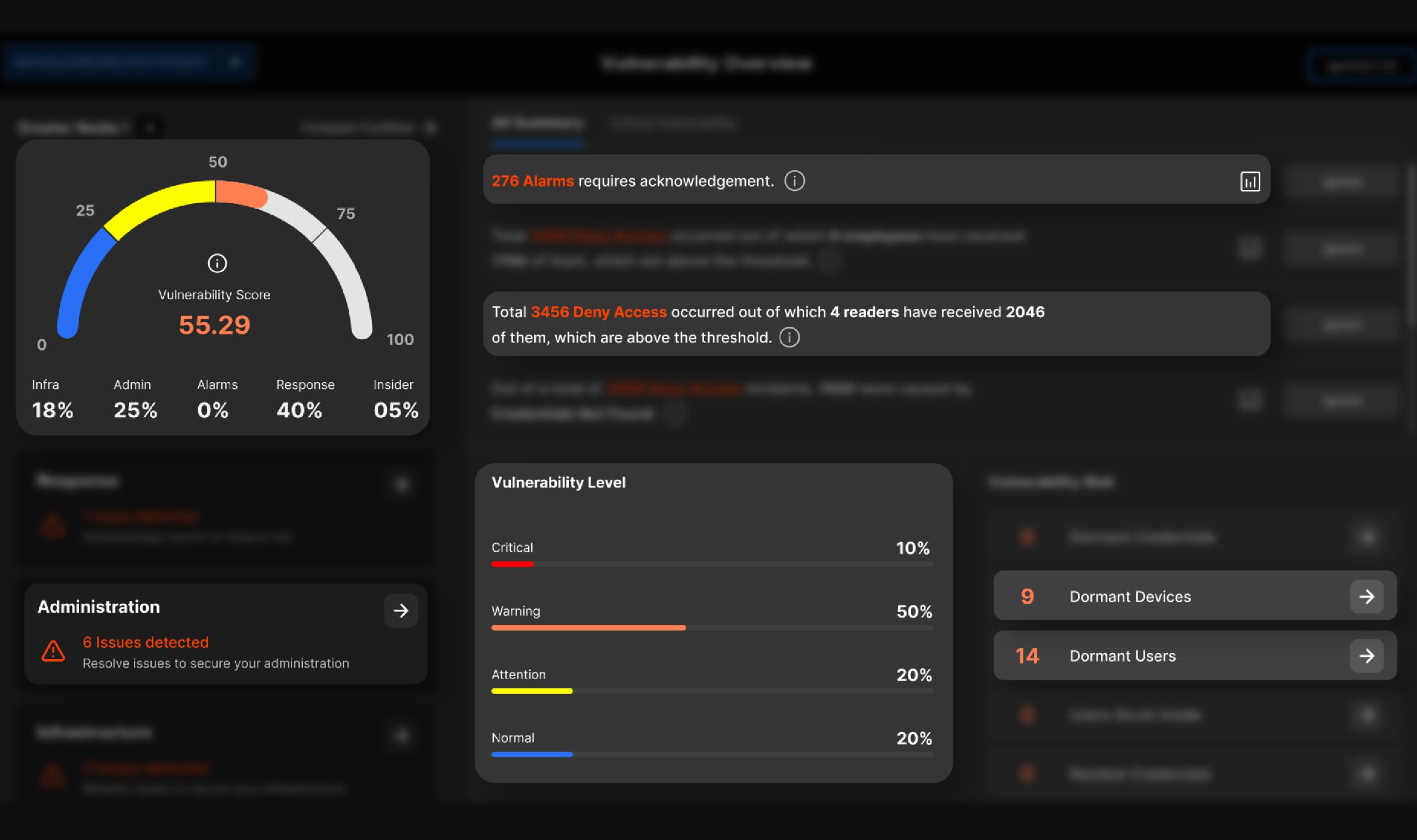
Ensuring robust security relies on swift decision-making and proactive actions to mitigate risks before they escalate. In today’s fast-paced environment, delays in threat detection and response can lead to significant vulnerabilities and potential breaches.
Managing security for large enterprises is no small feat. Security teams face a constant influx of alarms, overwhelming amounts of data, and the ongoing challenge of maintaining compliance with safety protocols. These demands consume valuable time and resources, making it difficult to stay ahead of threats.
That’s where AI and Machine Learning (ML) step in. By automating manual data analysis, streamlining security operations, and providing real-time, actionable insights, AI-powered solutions enable businesses to reduce workload, eliminate inefficiencies, and gain comprehensive visibility into their security landscape. With an intelligent, unified view of all access points, activities, and vulnerabilities, teams can swiftly identify and neutralize threats before they escalate—enhancing overall security effectiveness.
Enquiry Form
Please fill out the form below and we will contact you shortly
Eliminate time-consuming, manual processes with IDCUBE AInsights

GenAI-powered chatbot “AIsha”
provides instant assistance, reducing the time spent on routine access control queries such as identifying personnel presence, managing access rights, and retrieving historical data.

AI-driven dashboards
replace manual audits by offering real-time analytics on alarms, attendance, visitor trends, and credential management.
Predictive analytics
minimizes the need for frequent manual security assessments by automatically identifying vulnerabilities and potential threats.
On-the-go access credential issuance
No more delays coordinating with logistics, vendors, or smart card manufacturers. Issue and manage credentials instantly.
Unified credential dashboard experience
Gain real-time visibility into the credential distribution matrix and lifecycle, all in one place, without dealing with complex reporting structures.
With AI-driven automation, what once took hours can now be completed in minutes.
Reduce or Mitigate Headache
Security and system management should be effortless—not a burden.
Proactive security insights
help organizations prevent security breaches instead of merely reacting to them.
AI-powered threat detection
identifies and categorizes risks, allowing security teams to act before incidents occur.
Vulnerability detection
automatically flags misconfigurations, excessive access rights, and infrastructure weaknesses, ensuring a secure system without constant manual oversight.
Automated compliance and reporting
streamline regulatory adherence, eliminating the stress of audits and manual documentation.
One-click system understanding
Identify on-field devices in seconds, reducing the need for months of surveys and streamlining investment tracking.
Instant access to system details
Retrieve system information, serial numbers, and complete configurations with just a few clicks.
Mobile-based visitor card issuance
Improve the user experience and save time by issuing visitor credentials from a mobile device, eliminating the need for complex desktop UIs or security reception counters.
Remote system management
No need to be on-site for system configuration and monitoring. Manage everything securely over the cloud, saving valuable operational time and resources.
With IDCUBE AInsights, managing access control is seamless, efficient, and stress-free.
AI/ML Handle the Heavy Lifting
Transform security operations with data-driven intelligence.
Machine learning algorithms
analyze billions of access logs to detect patterns, anomalies, and security risks.
Behavioral analytics
assigns risk scores to users based on historical activity, helping identify insider threats effortlessly.
Automated facility security scores
assess over 50 security parameters, giving an objective overview of vulnerabilities.
AI-driven response systems
ensure critical alarms are acknowledged and acted upon, reducing human oversight burden.
Scalability that human efforts can’t match
A customer with 10,000 users generates 3.245 million logs per month and 35-50 million logs annually—analyzing this manually is impractical.
AI contextualizes data
Machine learning proactively predicts patterns, providing actionable insights on systems, processes, and user behavior without human intervention.
Real-time threat mitigation
Millions of access logs—cards, readers, inputs, and outputs—are continuously monitored and analyzed in real time, enabling early detection and prevention of security threats.
By leveraging AI and ML, IDCUBE AInsights ensures that businesses stay ahead of risks while reducing operational effort.
Connect with our team
Please complete the form below and our expert will contact you
To ensure prompt and efficient resolution of your issue, please provide the following details in your support ticket
Access your download instantly
Fill out the form below to download the file

Submit form to download Case studies
Submit form to download Case studies
Access your download instantly
Fill out the form below to download the brochure










