Why traditional Access Control blinds you to real threats and how to see them
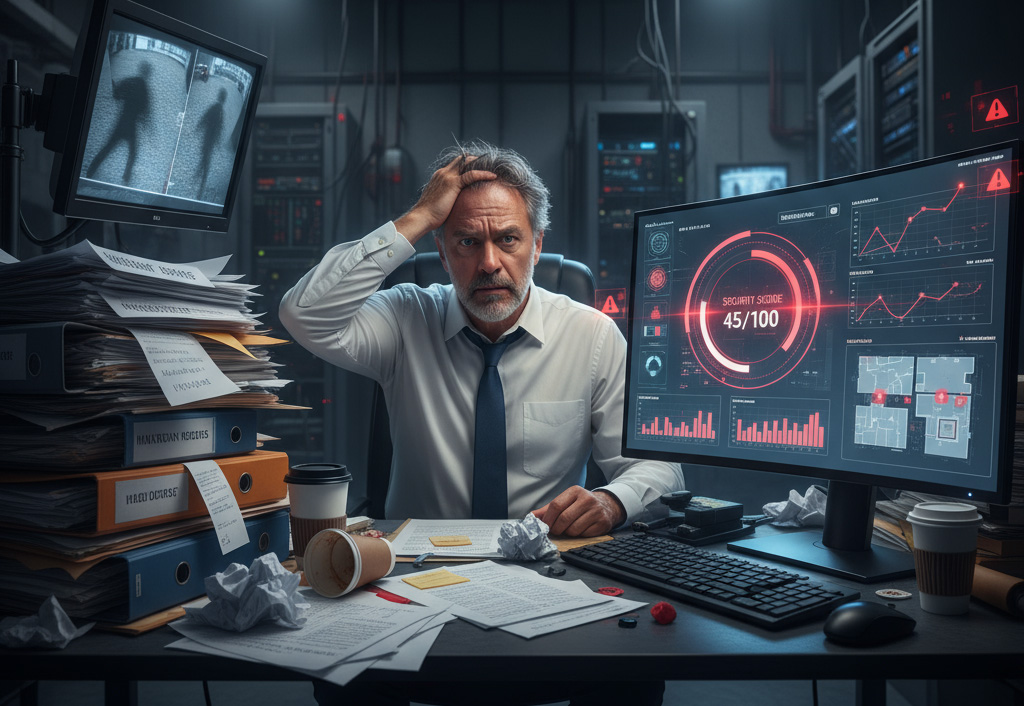
It was a Monday when Michael, the facility manager, got the call: someone had entered the building last night, and no one knew who. The CCTV had failed, leaving him with nothing but endless access logs provided by his access control software. Hours of manual analysis finally revealed the culprit: a dormant credential from an employee who’d left months ago. Michael realised audits hadn’t been done in ages, and with 20 sites to manage, enforcing policies was overwhelming. Alerts piled up, most unresolved, leaving him blind to his true security posture. Staring at the noise, he wished for clear answers in seconds.
When logs become overloaded
Modern business access control systems are excellent at recording everything. Every swipe, denied entry, forced door, or door held open too long gets logged. At first, this seems useful, but it quickly becomes overwhelming.
A mid-sized organisation can generate millions of records every month, millions of lines stripped of context. When something suspicious happens, the information exists but is buried. Security teams can’t quickly ask: Who was there? What changed? What’s unusual? Instead, they dig through spreadsheets while time runs out.
The invisible risk
Hackers make headlines, but insiders often pose the bigger danger. Employees, contractors, and vendors already carry credentials. They don’t need to break in, they swipe badges they shouldn’t have, stay late without reason, or subtly change routines.
These threats are the hardest to catch because they look normal. Traditional systems can record the act but never question the intent.
No way to measure
Michael managed five buildings. On paper, each was secure. But were they equally secure? Were some improving while others slipped? Dormant accounts piled up, response times varied, and alerts went unanswered.
Without a unifying score, there was no benchmark, no way to measure security posture across sites. It was like running a business without a balance sheet.
Hidden gaps
Even the basics weren’t reliable. Some accounts stayed active months after use. A few employees had excessive permissions. System connections weren’t always encrypted. Backups failed. Alarms triggered but were dismissed or lost in the flood.
The system wasn’t broken, but it wasn’t connecting the dots. Small oversights quietly piled up into vulnerabilities.
Questions without answers
Simple questions like- Who was in the lab after 7 PM? Which site responds slowest? Whose badge hasn’t been used in weeks? – takes a lot of time to answer.
The information existed, but it required specialists to export, decode, and compile. By the time answers arrived, it was often too late.
IDCUBE’s AInsights
This is where IDCUBE’s AInsights changes the story. Its machine learning models cut through millions of records in seconds, surfacing anomalies and vulnerabilities before they escalate. Through behavioural analysis, it learns what “normal” looks like and flags deviations, late-night access, unusual movement, and credential misuse, highlighting and ranking risky profiles that demand attention. For the first time, leaders can view a Security Score for each facility, similar to a credit score for physical security, making posture measurable, comparable, and trackable across sites.
And it doesn’t stop there. With AIsha, the GenAI chatbot, security teams don’t need to decode spreadsheets or wait for reports. They can ask, “Who stayed late after 9 PM?” or “Which site has the most dormant users?” and get clear, actionable answers in seconds.
AInsights finally gives commercial access control what it has always lacked: the intelligence to not just record what happened, but to explain it, measure it, and predict what might happen next.
And maybe, just maybe, that means facility managers like Michael can finally enjoy their Monday coffee in peace.
To know more about AInsights or see it in action, drop a message at nimish@idcubesystems.com.










